Understanding RSA
Setting the Stage
WIPI want this paper and exercise to be fun and enlightening for everyone.
I will try to make it fun and easy to follow along without glossing over too much of the underlying maths.
That being said, if this is not for you, or you just hate math, I encourage you to still try.
I will be adding python code blocks you can run as we move through the paper which I hope will make it more interactive and engaging.
So what is RSA?
We can't start talking about what RSA is without first paying homage to the creators, where it gets its name.
Ron Rivest, Adi Shamir, and Leonard Adleman collaborated and invented this public key system back in 1977, which in of itself really
does show its stability since it is still used widely today. RSA as I said before is a public key system or also known as an
Asymmetric encryption. This basically means that the encryption key is actually made public for everyone to use, called a public keys
then a 2nd decryption key us held privately by the owner, simply named a private key.
But I am sure many of you know this and thats not why you are here, you are here for the Juicy bits
Defining the Language
As with most mathematics, someone a while ago decided to use fancy letters to represent things, probably as a way to flex their
intelligence... I'm joking for the most part, normally this is done to help differentiate between different types of mathematics.
I plan on doing some First order Logic papers eventually and you will see what I mean by that then.
ANYWAY... Lets just make a table we can refer back to later to help.
| Symbol | Meaning | Do we Keep it Private? |
|---|---|---|
| p | Prime #1 | TRUE |
| q | Prime #2 | TRUE |
| n | n = p * q | FALSE |
| φ(n) | φ(n) = (p-1) * (p-1) | TRUE |
| e | pick any integer where 1 < e < φ(n) AND e is a coprime of (n AND φ(n)) | FALSE |
| d | where d*e(mod φ(n)) = 1 | TRUE |
Now, I will gloss over the phi function here but if you want to learn more as to where it comes from there are links at the bottom
e and d (for encryption and decryption) on the other hand needs some explaining but hang with me we have some tricks.
The first part of e is simple enough, we need a integer that is between 1 and φ(n) which at this point we know. The second part however, what does coprime mean, well in this case it means it shares no common factors with both n and φ(n). Now what we can do to simplify this is to just say e must be prime, and not a divisor of φ(n) (or if you divide φ(n) by e you do not get a whole number), which we can do some quick checks to be sure.
For d what we need to find a value that results in multiplying it by e and then doing mod φ(n) which gives us 1. I will go into how to find this in our first example.
To clear the air incase anyone is rusty or does not know what 'mod' means it basically is a remainder function, you shove a number into a mod(n) and you get out what is left over. I like to picture it like a clock which is mod(12). So if you know military time you kind of do this already, 1400 hours is actually 14 mod(12) which is 2, or 2pm. You count up to 12 and then start back over so 5 mod(3) would be 2, and 12 mod(5) would be 2 like 1,2,3,4,5,1,2,3,4,5,1,2
Example Please...
OK you stuck with me this long lets generate some keys. For this first one we will start with really small prime numbers. Clearly this is a terrible idea since the smaller our starting primes are the easier it is to crack, but the math is still the same and it is faster and easier to follow along.
- Pick 2 primes, our p and q, let's say 67 and 79
- Generate n by multiplying p and q to get 5293
- Generate φ(n) by multiplying p-1 and q-1 to get 5148
- For e, pick a prime number between 1 and 5148 and is not a divisor of 5148, let's go with 17
- For d we find a value where d*e(mod φ(n)) = 1, lets go with 1817
OK, now you might be asking, how the hell did I get 1817 for d, the question feels kind of brute forced. Well this is where I used the first bit of python code we really kind of need.
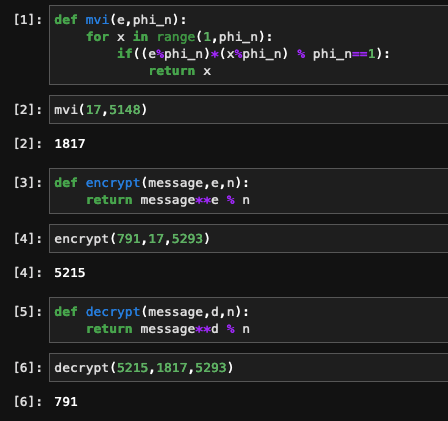
def mvi(e,phi_n):
for x in range(1,phi_n):
if((e%phi_n)*(x%phi_n) % phi_n==1):
return x
I called this mvi which is short for Modular Multiplicative Inverse, which I will also kind of gloss over as well, but I wanted you to see that you don't need to manually guess and check, this (although kind of doing that) does it really fast for you.
So now we have our numbers, let't table them back out
| Symbol | Value |
|---|---|
| p | 67 |
| q | 79 |
| n | 5293 |
| φ(n) | 5148 |
| e | 17 |
| d | 1817 |
Great now what...
Well now the fun starts, again we are kind of doing this by hand so rather than starting with a string and converting it to a number to encrypt then send and then decrypt then convert back into a string lets just encrypt a number using our new keys
First we need to send our Pub key to Alice, this is the pair of numbers e and n, so we will send her (17, 5293). Again this is public, so we can send this however we like, as long as we are sure its not messed with on the way.
Now Alice will send us a secret number by encrypting a clear number using this public key and that is done with the following function
def encrypt(message,e,n):
return message**e % n
Thats it, so in this case let's send 791, so we do encrypt(791,17,5293) which results in 5215
Bob gets 5215 and needs to decrypt it and that is done with this function
def decrypt(message,d,n):
return message**d % n
This is almost the same but we swap out the e for the d, and if we plug in decrypt(5215,1817,5293) we get, you guessed it, 791
And to show Im not making this up...
So you seen some stuff
This was a very high level and I did for sure gloss over some things but the math is there and I encourage you to look at what I have shown here and ask yourself some questions, challenge yourself
- Can you see any potential issues, how would you get past them?
- Can you update the functions to use strings not just numbers?
- In our example what happens if I picked the number 31337?
If you liked this please let me know back in the community post where I linked this, if you have questions or want more let me know that too.
More Links
I said I would
- https://en.wikipedia.org/wiki/RSA_(cryptosystem)
- https://en.wikipedia.org/wiki/Modular_multiplicative_inverse
- https://yewtu.be/watch?v=-ShwJqAalOk
- https://yewtu.be/watch?v=JD72Ry60eP4
- https://yewtu.be/watch?v=S9JGmA5_unY
- https://yewtu.be/watch?v=O4xNJsjtN6E